Threats
Ameaças em destaque do mundo digital
Raccoon Stealer upgraded to steal cryptocurrency and financial information
Raccoon stealer, a malware-as-a-service, will now try to steal your cryptocurrency. The malware is not spread through spam emails as previous Raccoon Stealers, but instead distributed as disguised installers for cracked and pirated software.
Type: Malware
Category: Typical malware
Severity: MEDIUM
Date: Aug 3, 2021

LockBit ransomware is now using Active Directory group policies to encrypt Windows domains
A new version of the LockBit 2.0 ransomware has been found that automates the encryption of a Windows domain using a PowerShell script to push a new group policy to all the workloads in the Active Directory group.
Type: Malware
Category: Ransomware
Severity: MEDIUM
Date: Jul 28, 2021
XLoader malware now targets Mac in addition to Windows
The XLoader trojan, which is the third most common malware, and commonly steals credentials and runs additional malicious payloads on Windows computers has been ported to work on MacOS. The Mac version is a port of the newer XLoader strain of FormBook, and is available on underground forums for as little as US$49 for a one-month license, making it very accessible to cybercriminals.
Type: Malware
Category: Typical malware
Severity: MEDIUM
Date: Jul 22, 2021

Olympics-themed malware found wiping files on infected computers
A Japanese security firm has discovered malware circulating that is wiping computers ahead of the Tokyo 2020 Olympic Games. The wiper is a .exe file that is designed to look like a PDF, claiming to be urgent information regarding cyber attacks associated with the Olympics.
Type: Typical malwar
Category: Malware
Severity: MEDIUM
Date: Jul 22, 2021

8th Chrome Zero-Day Vulnerability This Year Being Actively Exploited
Google Chrome's V8 JavaScript and WebAssembly engine has a type confusion vulnerability, tracked as CVE-2021-30563, that is actively being exploited in the wild. This vulnerability can lead to an attacker being able to run arbitrary code on affected devices. A patch is available and should be implemented immediately.
Type: Vulnerability
Category: Security update
Severity: MEDIUM
Date: Jul 16, 2021

Malware Caught Using OBS Studio to Spy on Victims
A new remote access trojan (RAT), called BIOPASS, has been using JavaScript embedded in gambling website support forums to trick users to install fake software updates that contain the trojan. Among typical trojan features that allow for persistent access and data theft, BIOPASS uses the popular streaming software OBS Studio to capture screen recordings on victim machines.
Type: Malware
Category: Typical malware
Severity: MEDIUM
Date: Jul 13, 2021

Windows Print Spooler Remote Code Execution Vulnerability
Proof-of-concept exploit code has been published online today for a vulnerability in the Windows Print Spooler service that can allow remote code execution to take place in compromised Windows systems. Tracked as CVE-2021-1675, the vulnerability was patched earlier this month in the Microsoft June 2021 Patch Tuesday security updates. Please update your Windows system to ensure the security of your system.
Type: Vulnerability
Category: Advisory
Severity: HIGH
Date: Jul 11, 2021

New attack campaign utilizing leaked Babuk Locker ransomware builder
A leaked Babuk Locker builder tool used to create custom ransomware executables is now being utilized by another threat actor in a very active campaign targeting victims globally. The threat actor has modify the enclosed ransom note to include their own contact info, and then run the build executable to create customized ransomware encryptors and decryptors that target Windows, VMware ESXi, NAS x86 and NAS ARM devices.
Type: Malware
Category: Ransomware
Severity: MEDIUM
Date: Jul 11, 2021
Self-propagating Indexsinas SMB worm spreads over few sectors including Cryptomining industry
The recent self-propagating computer worm called Indexsinas SMB was found to caused wide damages to several sectors in the community including telecommunication, healthcare and cryptomining industry. Researcher has found out that three Equation Group exploits were used during the propagation of the worm which includes EternalBlue, EternalRomance and DoublePulsar.
Type: Malware
Category: Malware
Severity: MEDIUM
Date: Jul 11, 2021

Hundreds of Companies Hit By Supply-Chain Ransomware Attack Served Through Kaseya VSA
In what appears to be a supply chain attack, Kaseya's remote management software was exploited by the REvil ransomware gang to ransom hundreds of businesses at once. Any organization using an on-site Kaseya VSA server should immediately shut down the server, as the first action taken in the attack is to disable administrator access to the server.
Type: Malware
Category: Ransomware
Severity: MEDIUM
Date: Jul 11, 2021

Hundreds of Companies Hit By Supply-Chain Ransomware Attack Served Through Kaseya VSA
In what appears to be a supply chain attack, Kaseya's remote management software was exploited by the REvil ransomware gang to ransom hundreds of businesses at once. Any organization using an on-site Kaseya VSA server should immediately shut down the server, as the first action taken in the attack is to disable administrator access to the server.
Type: Malware
Category: Ransomware
Severity: MEDIUM
Date: Jul 5, 2021

New Golang Remote Access Trojan (RAT) named ChaChi used in PYSA ransomware attacks
The ChaChi RAT has been created in the Go language and is currently used by the PYSA ransomware group against US schools. The current version of the RAT implements backdoor capabilities, DNS tunneling and allows attackers to harvest credentials. The RAT is obfuscated with the gobfuscate tool.
Type: Malware
Category: Typical malware
Severity: MEDIUM
Date: Jun 24, 2021
The Clop ransomware is back, after law enforcement made some arrests
The Clop ransomware operation is back in business after recent arrests. After about a week of low activity, the ransomware gang has sprung back into action yesterday after releasing the data for two new victims on their ransomware data leak site.
Type: Malware
Category: Ransomware
Severity: MEDIUM
Date: Jun 23, 2021

Paradise Ransomware source code released on a hacking forum
The complete source code for the Paradise Ransomware has been released on a hacking forum allowing any would-be cyber criminal to develop their own customized ransomware operation.
Type: Malware
Category: Ransomware
Severity: MEDIUM
Date: Jun 15, 2021

Chrome Zero-Day Vulnerability Being Actively Exploited
A high severity vulnerability in Google Chrome (CVE-2021-30551), caused by a type confusion issue in the V8 JavaScript engine, is actively being exploited in the wild. Google has released an update to patch this vulnerability, along with 13 other medium to critical severity vulnerabilities.
Type: Vulnerability
Category: Security update
Severity: MEDIUM
Date: Jun 10, 2021

Fujifilm Sufferes Suspected REvil Ransomware Attack
Fujifilm has shut down some of their networks after a ransomware attack on June 1st. REvil is suspected to be behind the attack, partially due to the Qbot trojan being used in the initial stage of the attack. As Fujifilm has chosen not to pay the ransom, stolen data will likely show up on a ransomware leak site in the next few days.
Type: Malware
Category: Ransomware
Severity: MEDIUM
Date: Jun 4, 2021
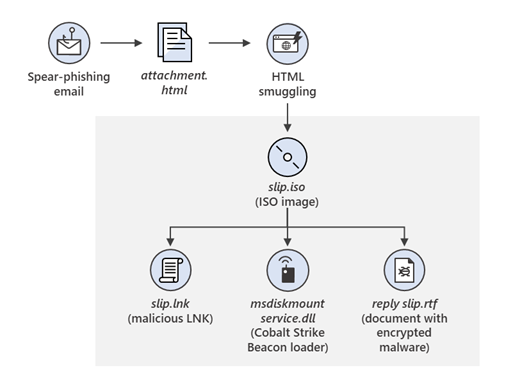
Threat actors behind SolarWinds attack are now spear phishing
The threat actors behind the massive SolarWinds attack has been discovered to be operating a spear-phishing campaign. The group recently began using a compromised Constant Contact account to send tailored phishing emails. The spear phishing email contains a malicious HTML attachment which drops an ISO image containing further malware.
Type: Malware
Category: Typical malware
Severity: MEDIUM
Date: May 28, 2021

New RAT fakes being ransomware
Microsoft Security Intelligence has released information regarding a remote access trojan, named StrRAT, that masquerades as ransomware. This RAT steals browser credentials, logs keystrokes, can remotely control your systems, and also renames files to appear they have been ransomed. Files renamed .crimsom are an indicator of compromise.
Type: Malware
Category: Typical malware
Severity: MEDIUM
Date: May 27, 2021

Zeppelin Ransomware Returns
After a brief hiatus, Zeppelin ransomware has resumed activity. The team behind this ransomware relies on more traditional attack vectors such as RDP and VPN vulnerabilities or phishing. Due to Zeppelin's sale model, new variants and the downloaders they use can be hard to initially detect.
Type: Malware
Category: Typical malware
Severity: MEDIUM
Date: May 25, 2021

Researchers have discovered a new banking malware from Brazil named Bizarro
Bizarro is a new banking trojan family originating in Brazil, that is now also in other countries. Cybercriminals behind this malware family are adopting various technical methods to complicate malware analysis and detection, as well as social engineering tricks that help convince targets to give out their online banking credentials. Bizarro is distributed via MSI packages downloaded by victims from links in spam emails. Once launched, Bizarro downloads a ZIP archive from a compromised website to implement further malicious functions.
Type: Malware
Category: Typical malware
Severity: MEDIUM
Date: May 21, 2021

Microsoft warns of data stealing malware called STRRAT that pretends to be ransomware
This RAT is infamous for its ransomware-like behavior of appending the file name extension .crimson to files without actually encrypting them. The new wave of attacks, commences with spam emails sent from compromised email accounts with 'Outgoing Payments' in the subject line, luring the recipients into opening malicious PDF documents that claim to be remittances, but in reality connect to a rogue domain to download the STRRAT malware.
Type: Malware
Category: Typical malware
Severity: MEDIUM
Date: May 21, 2021

CISA warns of new activity by the ransomware group called FiveHands
The US Cybersecurity & Infrastructure Security Agency (CISA) has warned organizations to be cautious of a relatively new ransomware group called FiveHands. FiveHands ransomware has been around since January 2021 and the group using it has been exploiting a zero day vulnerability in SonicWall VPN (CVE-2021-20016).
Type: Malware
Category: Ransomware
Severity: MEDIUM
Date: May 12, 2021

Shutdown of a Top U.S. Pipeline after Ransomware attack
Top U.S. pipeline, Colonial Pipeline, shuts down after DarkSide ransomware attack
Type: Malware
Category: Ransomware
Severity: MEDIUM
Date: May 10, 2021
